In October 2021, a post on the notorious 4chan site announced that hackers had stolen 126GB of source code and payment data from the popular video game streaming service Twitch. The culprit of the breach was the same as almost all cloud breaches—misconfiguration. Developers at Twitch had left an AWS S3 bucket unsecured. The attackers simply connected to it and downloaded the contents.
As a security practitioner, keeping a cloud environment secure is almost as difficult as getting it secure in the first place. When developers and their AI agents are racing to build applications, it is easy to ignore security until it’s too late.
In response to a wave of hacking incidents, AWS implemented a massive library of security improvements over the past few years. However, they only work if you deploy them, and it’s easy for customers to either not implement the relevant controls or turn them off when they become noisy.
Introducing Platformr’s New Security Module
Platformr already provides one of the fastest, most reliable ways to deploy an AWS environment that rigorously follows best practices. This creates a secure cloud foundation. However, merely having the right organizational structure and account access is only part of building a secure environment.
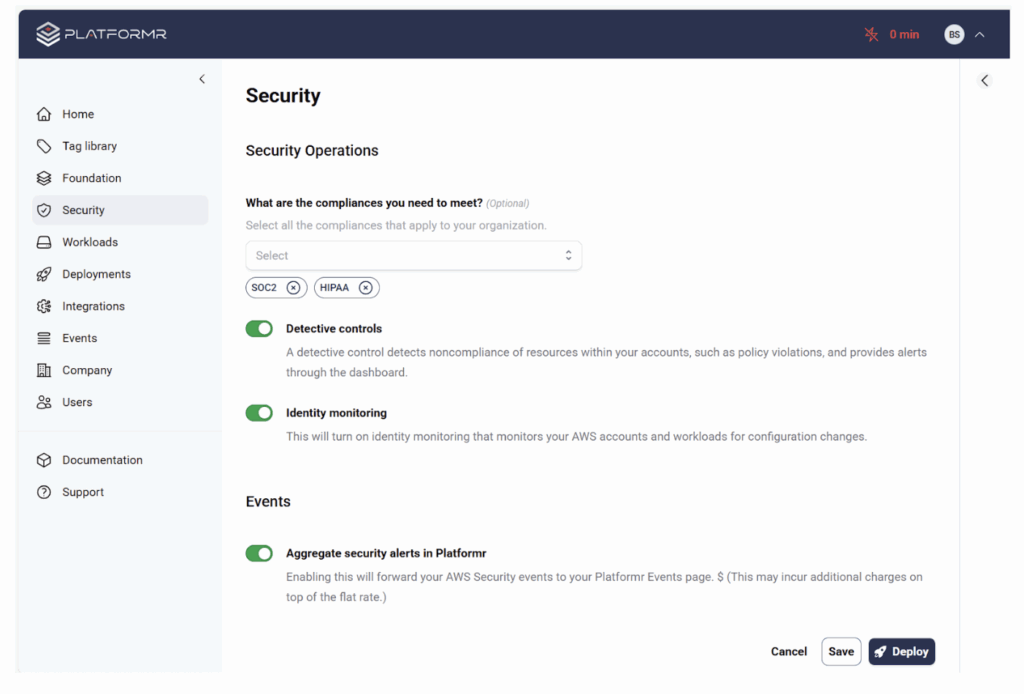
The next step is applying security configurations to the relevant AWS resources. Using Platformr’s Security Module, you can quickly and easily enable a huge set of security controls across your AWS Organization with just a few clicks.
Automating Guardrails with AWS Control Tower Controls
Platformr uses AWS Control Tower to automate the deployment and governance of security controls across your multi-account AWS environments with pre-configured blueprints called Control Tower Controls (CTCs).
There are three types of controls, which are predefined configurations for AWS services:
Detective: A control that identifies potential security vulnerabilities. These controls do not stop attacks, but can identify misconfigurations.
Preventative: A control that disables or prevents security vulnerabilities. These controls can stop attacks.
Proactive: A control that scans your resources and ensures they meet proper control requirements.
With hundreds of controls that can change often, managing and applying that long list can quickly get overwhelming. AWS organizes the controls into catalogs to help with implementation.
Using AWS Control Tower Control Catalogs to Help Meet Security Requirements
AWS Control Tower Control Catalogs (CTCC) are based on established security standards, such as HIPAA, PCI, NIST 800-171r2, or FedRAMP-r4. This allows you to quickly apply a set of controls to help your environment meet relevant security requirements. Even if your environment does not need to meet these compliance standards, you can use the control catalogs to apply best practices.
Additionally, AWS Control Tower provides tools to monitor for compliance with these standards. If a developer logs in and starts turning off security features, AWS Control Tower will detect it and notify you. CTC and CTCCs are a potent way to make sure your AWS environment starts and stays secure.
Platformr takes away one of the greatest impediments to cloud security – turning it on and making sure it’s done right in the first place.
Applying Security Controls with Automation
With the new Security Module, Platformr can accelerate and automate the process of applying controls (using the CTCCs) to targeted Organizational Units (OUs) or workloads. On the Security Tab, select the framework you want, click Detective Controls and then click Deploy.
The deployment takes from 10-30 minutes depending on how many frameworks you are adding. However, once these controls are in place, you have a base set of detective controls to monitor for security misconfigurations.
Enabling a Complete Set of Security Tools
AWS Control Tower Controls are not the only security controls Platformr deploys in its new Security Module. In order to implement these controls, Platformr also enables other security functions in AWS, including:
- AWS Inspector: Scans and analyzes vulnerabilities EC2 instances and containers.
- IAM Access Analyzer: Detects and monitors account access. Helps implement zero-trust and enforce least-privilege.
- AWS Guard Duty: Continuous monitoring of AWS resources for malicious activity.
- AWS Security Hub: Unified security operations console. Allows you to monitor the state of security controls and much more.
Enabling these services turns on a complete suite of security tools for your entire environment. Of course, you still need to monitor and manage these controls. However, Platformr takes away one of the greatest impediments to security in the cloud – turning it on and making sure it’s done right in the first place.
– Andrew Plato, CEO/Founder, Zenaciti
About the Author
Andrew Plato is an experienced CEO, founder, and author, as well as a pioneer in cybersecurity who redefined the industry’s landscape. Plato is the author of “The Founder’s User Manual: Practical Strategies for the Startup Leader” and a strategic advisor to Platformr.
Looking to improve security, visibility, and control across your AWS Organization?
Follow Us







